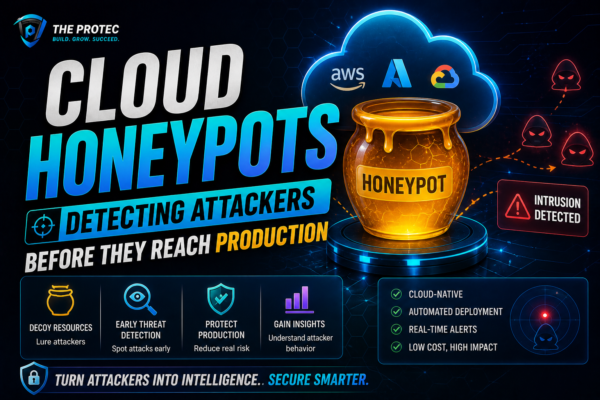
Cloud Honeypots: Detecting Attackers Before They Reach Production
Unlock advanced cyber threat detection by deploying cloud honeypots. Learn how strategic AWS honeypot setups help identify attackers early and protect your production environment.
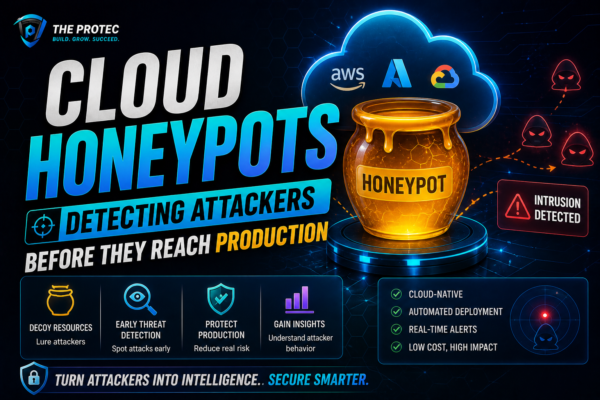
Unlock advanced cyber threat detection by deploying cloud honeypots. Learn how strategic AWS honeypot setups help identify attackers early and protect your production environment.