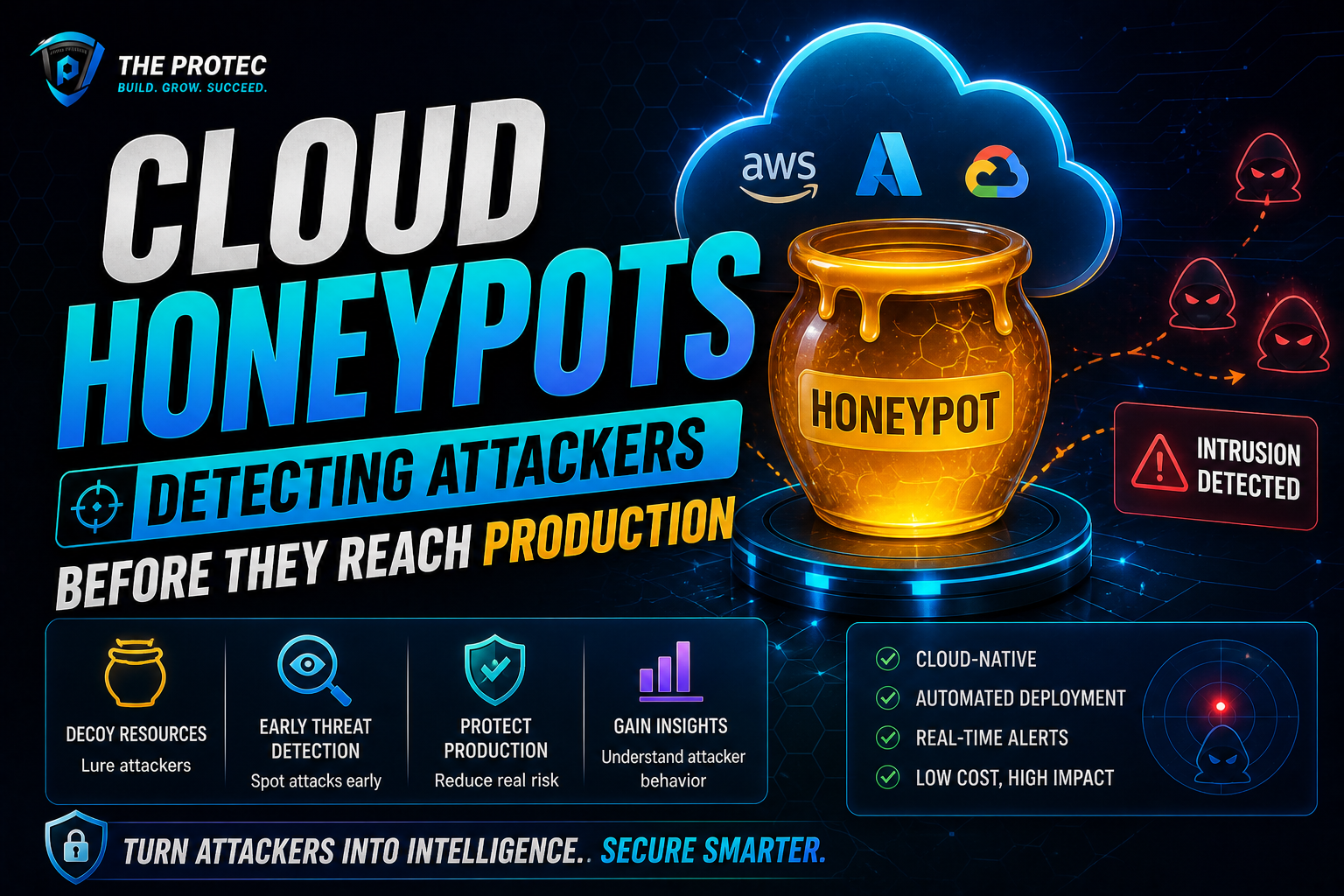
Introduction to Cloud Honeypots
In an era where cloud infrastructure becomes the backbone of enterprise IT, safeguarding these environments from cyber threats is a paramount concern for security teams. Traditional defenses like firewalls and intrusion detection systems are necessary but often insufficient to detect sophisticated attackers during the early stages of compromise. This is where cloud honeypots come into play. By deploying decoy resources designed to attract malicious actors, cloud honeypots provide valuable insights into attacker behavior and help security teams intercept threats before they escalate to production environments.
What Are Cloud Honeypots?
Honeypots, at their core, are deliberately vulnerable or seemingly valuable digital assets used to lure attackers. Unlike traditional honeypots placed on-premises, cloud honeypots run within cloud environments such as Amazon Web Services (AWS), Microsoft Azure, or Google Cloud Platform (GCP). These honeypots mimic real cloud workloads, services, or endpoints, enticing attackers by presenting attractive targets that do not expose actual production data or infrastructure.
By interacting with these decoy resources, attackers reveal their tactics, techniques, and procedures (TTPs), allowing security teams to detect, analyze, and respond promptly. The value of cloud honeypots lies in their ability to provide early warning signals and detailed cyber threat intelligence.
Why Deploy Cloud Honeypots for Cyber Threat Detection?
Cloud environments face unique security challenges. The dynamic scaling of services, multi-tenant design, and broad attack surface increase the risk of undetected breaches. Here’s how cloud honeypots address these challenges:
- Early Threat Identification: Honeypots are designed to be attacked. Any interaction typically signals malicious activity, enabling teams to spot adversaries lurking in the environment before real assets are impacted.
- Reduction of False Positives: Traditional security solutions like IDS can generate many alerts triggered by benign activity. Interactions with honeypots are likely malicious, providing highly accurate indicators.
- Understanding Attacker Behavior: Observing attackers’ methods on honeypots provides valuable insights into their strategies, helping teams tailor defenses accordingly.
- Protection of Production Resources: By diverting attackers to decoys, honeypots reduce exposure risk and buy time to initiate incident response measures.
Key Components of Effective Cloud Honeypots
An effective cloud honeypot must balance realism, stealth, and manageability. Key components include:
- Realistic Resource Emulation: The honeypot should mimic legitimate cloud services or workloads like web servers, databases, or APIs to convince attackers of its authenticity.
- Isolation from Production: Honeypots must be isolated to prevent attacks from spreading or affecting live environments.
- Logging and Monitoring: Comprehensive log capture and monitoring enable detection of suspicious activity and facilitate forensic investigations.
- Automation and Scalability: Cloud-native automation tools help deploy, scale, and reset honeypots efficiently, keeping pace with constantly evolving threats.
Step-by-Step Guide to AWS Honeypot Setup
AWS remains a leading cloud platform widely targeted by attackers, making it an ideal candidate for honeypot deployment. Here’s how organizations can set up an effective AWS honeypot:
1. Define Honeypot Objectives and Scope
Decide on the type of attack behavior you want to detect (e.g., reconnaissance, credential theft, lateral movement) and select appropriate honeypot types (low-interaction versus high-interaction). Consider whether the honeypot will simulate an EC2 instance, S3 bucket, or IAM roles.
2. Design the Honeypot Architecture
Architect the honeypot within a dedicated Virtual Private Cloud (VPC). Use subnet segmentation and security groups to tightly control inbound and outbound traffic, ensuring isolation from production workloads. Incorporate AWS-specific services, such as AWS CloudTrail and VPC Flow Logs, to track all interactions.
3. Deploy the Honeypot Resources
Launch decoy EC2 instances, configure fake S3 buckets, or set up decoy Lambda functions. For example, an EC2-based honeypot can run vulnerable or deprecated software to attract attackers. Assign realistic tags and naming conventions to avoid suspicion.
4. Configure Monitoring and Alerting
Integrate with AWS CloudWatch, GuardDuty, and Security Hub to collect detailed telemetry. Enable alerts on specific events such as unauthorized login attempts, unusual API calls, or data exfiltration behaviors. Use centralized logging solutions like AWS Elasticsearch or third-party SIEM tools for analysis.
5. Implement Automation and Recovery
Leverage AWS Lambda functions and Infrastructure as Code (IaC) tools like AWS CloudFormation or Terraform to automate honeypot deployment and recovery. Automated resets ensure the honeypot remains available and free from compromise artifacts that could mislead detection.
6. Analyze and Respond
Regularly analyze attacker interactions captured by the honeypot. Correlate honeypot data with broader cloud security telemetry to identify emerging threats. Use this intelligence to refine cloud security policies, patch vulnerabilities, and educate your security operations center (SOC) team.
Advanced Techniques and Modern Tools for Cloud Honeypots
With advancements in cloud technology and security, modern honeypots have evolved beyond simple decoy resources. Here are some techniques and tools gaining traction:
- Deception Platforms: Comprehensive deception suites integrate honeypots with lures and breadcrumbs across cloud resources to create a layered defense. Products like Cymmetria and Guardicore enable automated deployment of dynamic decoy assets.
- Serverless Honeypots: Deploying honeypots as serverless functions simulate cloud-native workloads such as AWS Lambda or Azure Functions. These capture attacker interactions with minimal infrastructure overhead.
- AI and Machine Learning: Integrating ML aids in analyzing honeypot logs to detect patterns and anomalies faster, improving threat detection precision.
- Integration with Cloud-Native Security Services: Combining honeypots with services like AWS GuardDuty, Microsoft Defender for Cloud, or Google Cloud Security Command Center amplifies detection and response capability.
Challenges and Considerations in Deploying Cloud Honeypots
While cloud honeypots offer undeniable benefits, deploying them also comes with challenges:
- Resource Costs: Running multiple honeypots, especially high-interaction types, incurs cloud compute and storage costs that must be justified.
- False Sense of Security: Honeypots are complementary tools, not complete solutions. Over-reliance risks neglecting comprehensive security hygiene.
- Detection Risk: Skilled adversaries may detect honeypots and avoid them or use them to feed false intelligence back to defenders.
- Security of Honeypots Themselves: A compromised honeypot could be used as a platform for further attacks if not properly isolated.
Best Practices for Maximizing Cloud Honeypot Effectiveness
To get the most from cloud honeypots, consider these best practices:
- Regularly Update and Rotate Honeypots: Keep honeypots up to date to reflect current production environments and attacker techniques.
- Integrate with Broader Security Stack: Ensure honeypot alerts feed directly into your SOC workflows and incident response plans.
- Use Multiple Honeypot Types: Deploy a mix of low- and high-interaction honeypots across different cloud assets to attract a wide attacker profile.
- Monitor Continuously: Active monitoring and rapid alert handling prevent attackers from leveraging the honeypot.
- Employ Automation: Automate deployment, scaling, and remediation using cloud-native tools to reduce manual overhead.
Frequently Asked Questions (FAQ)
What is the difference between a low-interaction and high-interaction cloud honeypot?
Low-interaction honeypots simulate limited protocols or services and capture only basic attacker interactions, requiring less maintenance and posing minimal risk. High-interaction honeypots mimic complete systems, allowing attackers to interact extensively, providing richer intelligence but with greater complexity and risk.
Can cloud honeypots detect insider threats?
While primarily designed to detect external threats, cloud honeypots can help identify insider threats if internal users interact with decoy resources inappropriately. For example, an employee probing unused or fake cloud resources may trigger honeypot alerts.
Are there pre-built AWS honeypot solutions available?
Yes, several open-source and commercial solutions exist for AWS honeypot deployment. Tools like Honeytrap, Cowrie (adapted for cloud), and managed deception platforms provide templates and frameworks to simplify setup.
Conclusion
Cloud honeypots represent a powerful proactive tool in the cyber threat detection arsenal. By deploying believable decoy resources within cloud environments, organizations gain the ability to detect and study attackers before they compromise production systems. As cloud infrastructures grow more complex and adversaries more sophisticated, integrating cloud honeypots with automated monitoring and response strategies becomes a vital component of modern cybersecurity defense.
Implementing an AWS honeypot setup offers a practical starting point for organizations looking to harness this technology. When combined with the latest deception platforms and analytics, cloud honeypots transform raw attack data into actionable threat intelligence, helping secure the gateway to your production environment.