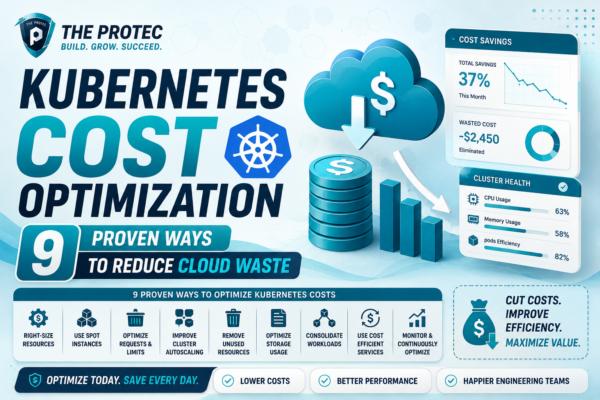
Kubernetes Cost Optimization: 9 Proven Ways to Reduce Cloud Waste
Optimize your Kubernetes deployments and reduce cloud spend with these 9 practical strategies and top K8s cost tools. Master cost-efficient cloud management today.
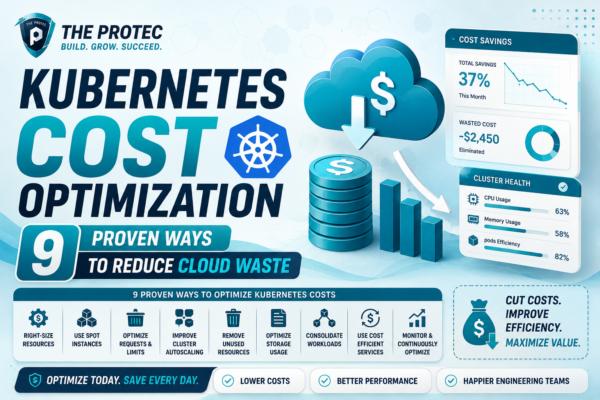
Optimize your Kubernetes deployments and reduce cloud spend with these 9 practical strategies and top K8s cost tools. Master cost-efficient cloud management today.