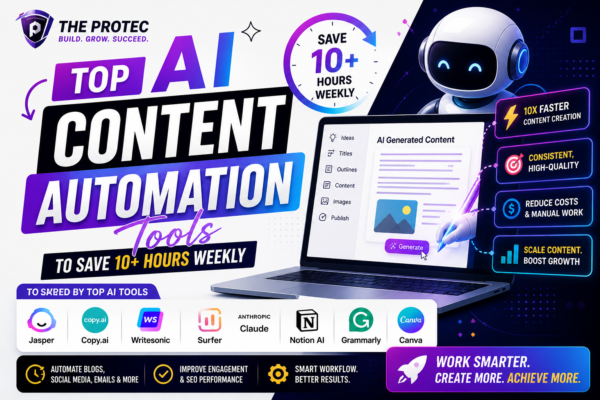
Top AI Content Automation Tools to Save 10+ Hours Weekly
Discover the best AI content automation tools that streamline your workflow and help you save over 10 hours weekly with proven productivity gains and use cases.
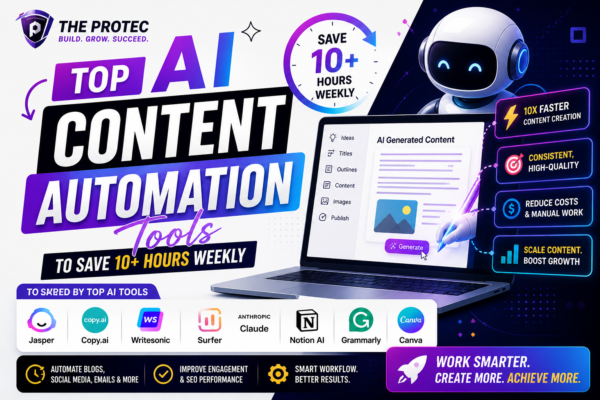
Discover the best AI content automation tools that streamline your workflow and help you save over 10 hours weekly with proven productivity gains and use cases.