Understanding GraphQL Security and the Risks of Overfetching
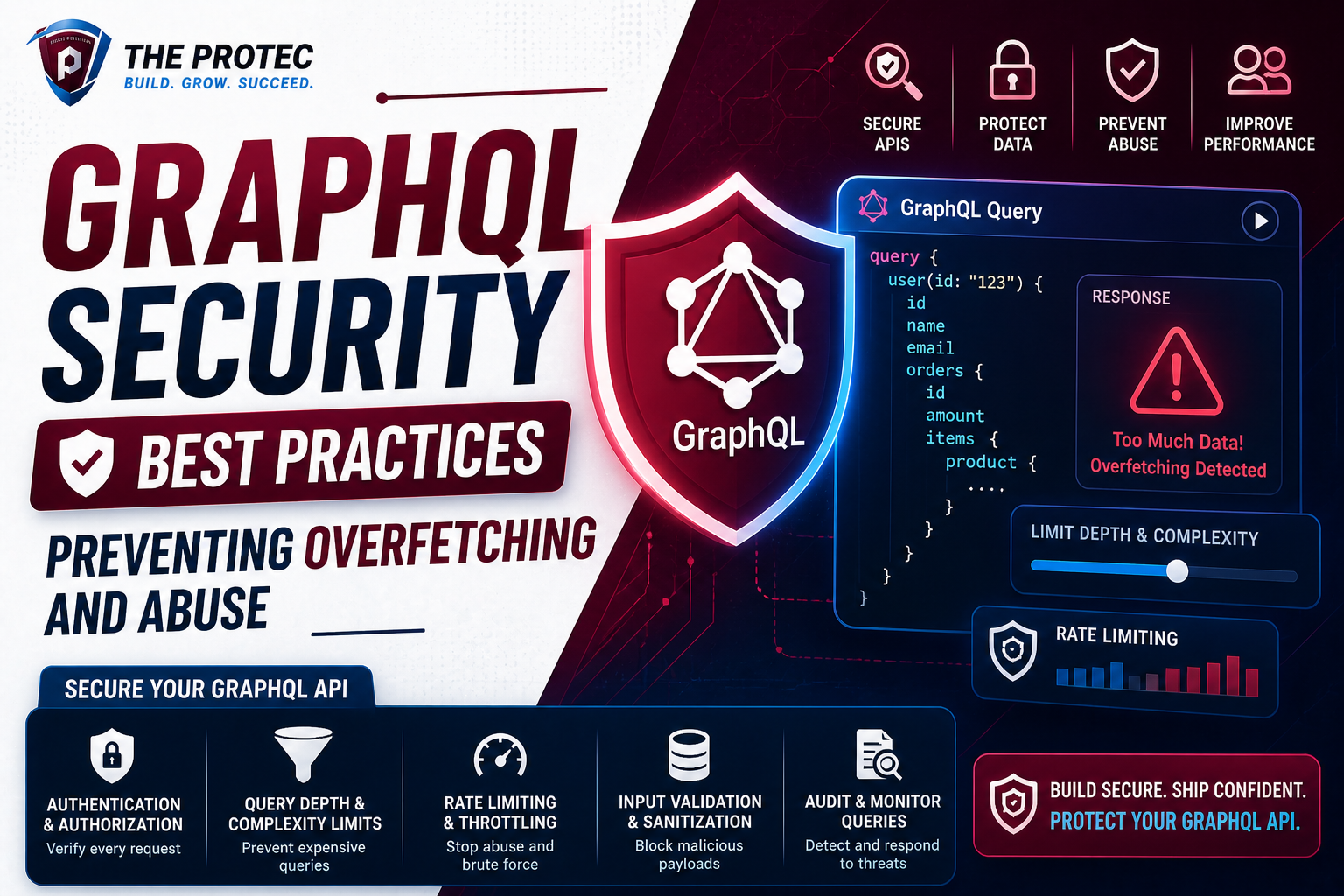
GraphQL offers powerful flexibility, enabling clients to request precisely the data they need. While this reduces payload size and improves performance, it also introduces unique security challenges. Chief among these concerns is overfetching a scenario where malicious or poorly designed queries request excessive data, potentially overwhelming backend resources or exposing sensitive information.
Unlike traditional REST APIs with fixed endpoints, GraphQL’s single endpoint and query language allow clients to craft complex nested queries, which can inadvertently cause heavy server load. This flexibility, if left unchecked, can lead to GraphQL security vulnerabilities, including denial of service (DoS) attacks through query complexity exploitation.
Key GraphQL Vulnerabilities: Query Complexity and Overfetching Exploits
To secure a GraphQL API effectively, it is critical to understand the primary vulnerabilities:
- Query Complexity Attacks: Attackers craft queries with deeply nested or recursive fields that dramatically increase execution time and resource consumption.
- Overfetching: Clients request more information than necessary, either unintentionally or maliciously, which can degrade performance and reveal unintended data.
- Introspection Abuse: Attackers use introspection queries to map out the entire GraphQL schema, discovering exploitable fields or sensitive data.
- Denial of Service (DoS): Excessive or resource-heavy queries can overwhelm the server, causing legitimate requests to fail.
Given GraphQL’s increasing adoption, these vulnerabilities are trending concerns among developers and security experts alike.
Implementing API Query Limits to Mitigate Abuse
A cornerstone of securing GraphQL endpoints is enforcing strict limits on API queries. These limits control the resources consumed by any single query and help prevent abuse.
1. Depth Limiting
GraphQL queries can be arbitrarily deep due to nested fields. Setting a maximum query depth restricts how many nested levels are allowed.
- Benefits: Limits recursive or overly nested queries that increase processing burdens.
- Implementation: Middleware such as graphql-depth-limit can be integrated into your server.
2. Complexity Scoring
Unlike depth, complexity scores estimate the real cost of a query based on fields, arguments, and nested queries.
- Benefits: Gives a more granular control by weighing fields differently based on their data-fetching impact.
- Implementation: Tools like graphql-query-complexity help measure and enforce custom complexity limits effectively.
3. Rate Limiting
Combining query limits with rate limiting protects your API from repeated abuse by throttling the client’s request rate.
- Benefits: Prevents brute force attacks and excessive API consumption.
- Considerations: Use IP-based or user token-based rate limiting depending on your authentication model.
Best Practices to Secure GraphQL Endpoints
Beyond query limits, layering additional security measures is essential:
1. Disable Introspection in Production
Disabling introspection queries in production environments prevents attackers from enumerating your schema, reducing information leakage.
2. Use Proper Authentication and Authorization
Ensure that sensitive data is protected by strict access controls. Leverage token-based authentication (e.g., OAuth, JWT) and implement field-level authorization to restrict data access within queries.
3. Whitelist Queries
Allow only pre-approved queries by implementing query whitelisting. This reduces the risk of maliciously crafted queries.
4. Monitor and Log Query Usage
Continuous monitoring sheds light on unusual query patterns that may indicate abuse or attempted attacks. Use logging to audit how users interact with your API.
5. Use Persisted Queries
Persisted queries reduce the risk of attacks by allowing only known, pre-registered queries to execute. They also improve performance by reducing parsing overhead.
Defending Against Query Complexity Attacks: A Practical Approach
Query complexity attacks exploit an API’s capacity to process expensive queries causing resource exhaustion. Practical defenses include:
- Establish Complexity Thresholds: Set conservative complexity budgets that reflect your backend’s capacity.
- Adaptive Throttling: Dynamically adapt query limits based on current load and usage patterns.
- Cache Expensive or Repetitive Queries: Caching results for frequently run complex queries mitigates their impact.
- Use Schema Design to Limit Complexity: Flatten deeply nested types and avoid exposing recursive or unlimited lists.
Recent Trends and Advanced Tools for GraphQL Security
With rapidly evolving GraphQL ecosystems, new tools and frameworks have emerged to bolster security:
- GraphQL Gatekeeper: An open-source proxy server that enforces authentication and query complexity limits before reaching your GraphQL server.
- GraphQL Shield: A flexible authorization layer that leverages schema directives to enforce field-level access controls.
- Introspection Query Filters: Packages that selectively allow or block specific introspection queries based on roles.
Organizations are increasingly adopting zero-trust models and advanced API gateways with integrated GraphQL support to offer holistic security.
FAQ
Q1: How does overfetching impact GraphQL API security?
Overfetching leads to excessive data retrieval, increasing server load and response time. It may also expose sensitive data if permissions are not enforced correctly, opening doors to information leakage or denial of service.
Q2: What is the difference between query depth limiting and complexity scoring?
Depth limiting restricts how deeply nested a query can be, while complexity scoring assigns weights to fields and arguments to estimate resource cost more precisely. Complexity scoring provides finer control over query validation.
Q3: Can rate limiting alone protect a GraphQL API?
Rate limiting helps but is not sufficient alone. Since even a single complex query may exhaust resources, combining rate limiting with query complexity and depth controls is essential for robust protection.
Conclusion
Protecting GraphQL APIs from overfetching, query complexity attacks, and abuse demands a multi-layered security approach. By enforcing API query limits, employing field-level authorization, disabling introspection in production, and utilizing modern security tooling, developers can secure their GraphQL endpoints against prevalent vulnerabilities.
As GraphQL adoption grows, staying updated on emerging threats and best practices is vital. Combining rate limiting, complexity analysis, and diligent monitoring enables teams to deliver performant, secure APIs that stand resilient under attack.