Introduction
As organizations increasingly embrace multi-cloud architectures to achieve agility, cost-efficiency, and innovation, they are simultaneously facing unprecedented security challenges. Multi-cloud security is no longer a niche topic; it’s a critical concern that IT and security leaders must address to protect data, applications, and infrastructure effectively. The reality is simple: the more cloud environments an organization employs, the greater the potential for security gaps, complexity, and risk exposure.
This article delves deep into why multi-cloud strategies, despite offering operational advantages, amplify security risks. We will explore the inherent complexity of managing multiple cloud platforms, the critical visibility issues that arise, and the emerging need for unified security strategies that can bridge disparate environments. Understanding these factors is key to advancing your organization’s cloud risk management capabilities and strengthening hybrid cloud security postures.
The Complexity of Multi-Cloud Security
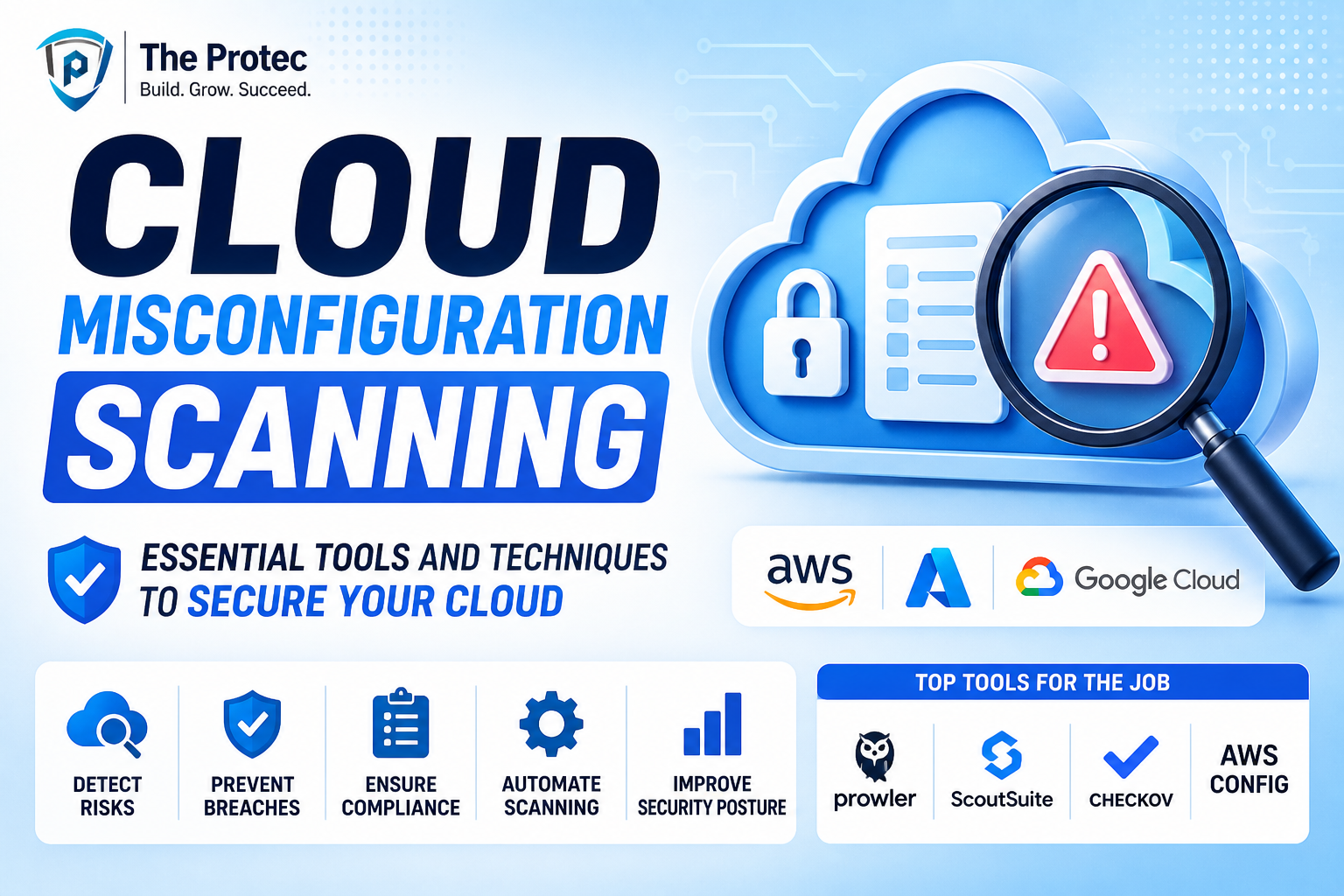
Organizations utilizing several cloud providers such as AWS, Microsoft Azure, Google Cloud Platform, and private clouds face a complex security landscape. Each environment brings its own set of tools, configurations, compliance standards, and security models. This diversity can quickly escalate management overhead and increase the likelihood of misconfigurations, which are the root cause of many cloud breaches.
Diverse Security Controls and Management Frameworks
Different cloud platforms offer distinct native security controls and policy frameworks. For example, AWS Identity and Access Management (IAM) differs fundamentally from Azure Active Directory in policy enforcement and permissions management. Security teams must become adept at interpreting and applying each provider’s controls, which adds layers of complexity and training requirements.
Shadow IT and Untracked Cloud Usage
Multi-cloud environments often suffer from shadow IT – the use of cloud services outside of official organizational oversight. When developers or business units bypass centralized IT governance, unknown cloud resources proliferate, adding unknown attack vectors and compliance blind spots. Maintaining a comprehensive inventory of assets across all clouds becomes a daunting, yet critical, task.
Disparate Compliance Requirements
Regulatory compliance requirements vary by industry and region and multi-cloud environments can make maintaining compliance more complicated. Different clouds might support distinct compliance certifications (e.g., SOC 2, ISO 27001, GDPR), but aligning internal policies across multiple providers multiplies challenges related to audits, reporting, and remediation.
Visibility Challenges in Multi-Cloud Security
Visibility is often cited as the cornerstone of security, and in multi-cloud environments, gaining end-to-end visibility is significantly more difficult. Without comprehensive oversight, threat detection, risk assessment, and incident response become reactive and fragmented.
Fragmented Monitoring and Logging
Each cloud provider has its own monitoring and logging tools with varying capabilities and data formats. Without integration, security teams can only view isolated segments of their environments. This fragmentation hampers the ability to detect lateral movement by attackers or abnormal behavior spanning multiple clouds.
Data Silos and Lack of Unified Dashboards
Data generated by cloud security controls and telemetry is often siloed inside individual cloud console dashboards. This isolation reduces situational awareness and delays threat identification. Creating unified dashboards that aggregate and normalize data from multiple clouds is a technical and operational challenge but essential for effective cloud risk management.
Inconsistent Policy Enforcement
Visibility deficits extend to policy enforcement as well. Without centralized visibility, deviations from security baselines can go unnoticed, leaving gaps that adversaries exploit. Organizations struggle to implement consistent identity and access management, encryption, and network security policies across heterogeneous cloud platforms.
Unified Security Strategies: The Path Forward
To overcome the multifaceted challenges of multi-cloud security, organizations are shifting towards unified strategies that harmonize security management across cloud providers. This approach enhances visibility, simplifies compliance, and reduces operational complexity.
Adoption of Cloud-Native and Third-Party Security Platforms
Leveraging cloud-native security tools with robust APIs allows organizations to automate and consolidate security operations. However, many companies find greater value in third-party multi-cloud security platforms that provide centralized policy management, real-time monitoring, and threat intelligence integration across multiple clouds.
Implementing Zero Trust Architectures
Zero Trust principles continuous verification of users, devices, and workloads regardless of location are becoming foundational to hybrid and multi-cloud security strategies. By enforcing least-privilege access and micro-segmentation, organizations reduce attack surfaces across sprawling cloud estates.
Automation and Orchestration to Reduce Human Error
Automation of routine security tasks like configuration checks, patching, and incident response reduces scope for human error, a leading cause of security breaches. Orchestrating such automation through security information and event management (SIEM) or security orchestration, automation, and response (SOAR) platforms enables faster, coordinated responses.
Unified Compliance and Risk Frameworks
Establishing unified risk management frameworks enables consistent policy enforcement and audit readiness across all cloud environments. Leveraging frameworks such as the Cloud Security Alliance’s Cloud Controls Matrix (CCM) alongside automated compliance reporting tools helps maintain oversight over diverse cloud deployments.
Best Practices for Effective Multi-Cloud Security
- Conduct Comprehensive Asset Discovery: Maintain an accurate, centralized inventory of all cloud resources, including ephemeral and shadow IT assets.
- Implement Centralized Identity Management: Use federated identity and single sign-on (SSO) solutions to simplify access control across clouds.
- Integrate Security Tooling: Aggregate logs and alerts from multiple clouds into a single platform for holistic threat detection.
- Establish Continuous Compliance Monitoring: Automate compliance tracking and reporting to identify and remediate gaps promptly.
- Invest in Staff Training: Ensure security teams are skilled in cloud platforms and multi-cloud security frameworks.
- Utilize Encryption and Data Loss Prevention (DLP): Apply consistent encryption standards for data at rest and in transit across every cloud.
Frequently Asked Questions (FAQ)
What is the biggest security risk in multi-cloud environments?
The greatest risk is the increased likelihood of misconfiguration and lack of centralized visibility, which creates gaps that attackers can exploit. Additionally, disconnected security tools and inconsistent policy enforcement further elevate risk.
How does hybrid cloud security differ from multi-cloud security?
Hybrid cloud security focuses on securing an infrastructure combining private and public clouds, often connected to on-premises data centers. Multi-cloud security involves managing security across multiple public cloud providers, which may or may not include private clouds. Both require distinct, but sometimes overlapping, strategies for managing complexity and risk.
What role does automation play in cloud risk management?
Automation reduces manual errors, accelerates configuration compliance, and enables rapid threat detection and response. Automated workflows help scale security operations efficiently in complex multi-cloud environments.
Conclusion
Multi-cloud environments offer undeniable benefits but come paired with significantly amplified security challenges. Complexity, lack of visibility, and disparate security mechanisms create fertile ground for increased cloud risk. However, by embracing unified security strategies leveraging automation, centralized monitoring, and zero trust architectures organizations can mitigate risks and safeguard their hybrid and multi-cloud assets.
As cloud adoption continues to evolve, staying ahead of security challenges requires proactive cloud risk management and a holistic approach to multi-cloud and hybrid cloud security. Forward-thinking companies invest strategically in people, processes, and technology to ensure their multi-cloud journey remains secure, compliant, and resilient.
For additional insights on multi-cloud security and the latest best practices, visit Cloud Security Alliance.