5G vs 6G: What the Next Generation of Connectivity Means
Explore the differences between 5G and 6G, their speed, latency, applications, and what the next generation of connectivity means for industries and daily life.





Learn how to build a SaaS app without coding using AI-powered no-code tools. This step-by-step guide walks you through modern platforms to launch your SaaS quickly and efficiently.

Explore advanced secrets management for cloud-native applications, comparing vault systems, encryption strategies, and runtime secrets injection beyond environment variables.
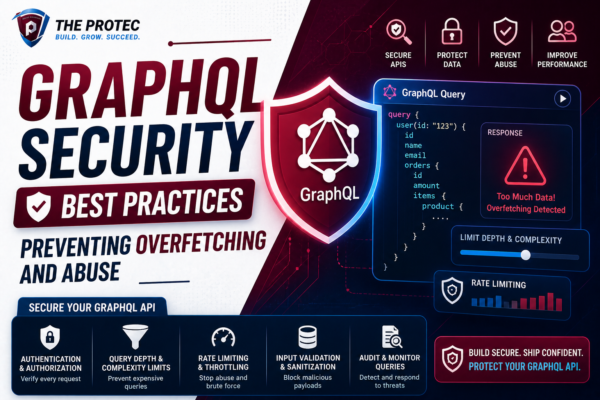
Explore expert strategies to safeguard GraphQL APIs against overfetching, query complexity attacks, and abuse with proven security best practices.

Discover the top website speed optimization tools proven to improve Core Web Vitals metrics and boost SEO performance with real-world benchmarks and expert insights.

Discover the top business password managers designed for teams, focusing on pricing, features, and ease of use to enhance team security tools seamlessly.
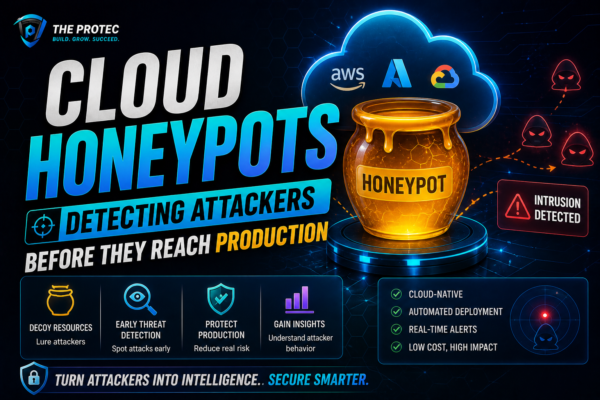
Unlock advanced cyber threat detection by deploying cloud honeypots. Learn how strategic AWS honeypot setups help identify attackers early and protect your production environment.

Discover how browser isolation technology is revolutionizing secure browsing by preventing malware and phishing attacks through remote browser security.

Discover how eSIM and iSIM technologies are transforming mobile network tech, marking the end of traditional SIM cards and reshaping device connectivity.
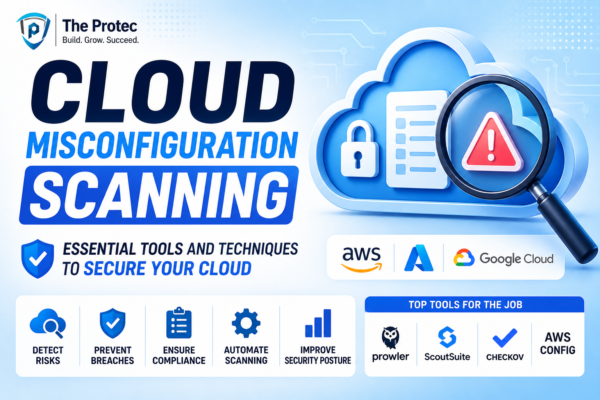
Discover how to identify and fix cloud misconfigurations with top AWS security scanning tools and strategies to protect your cloud infrastructure from vulnerabilities.

Explore five impactful cyber attacks that challenged organizations recently, and learn actionable strategies to enhance your cybersecurity and prevent data breaches.