
AI in Climate Tech: Fighting Environmental Challenges with Innovation
Discover how AI in Climate Tech is revolutionizing energy optimization, predictive climate modeling, and carbon capture to combat global environmental challenges.







Explore the potential of AI code review using LLM coding tools, evaluating their strengths, weaknesses, and real-world limitations compared to senior developers.

Passkeys vs Passwords: Why Passkeys Are the Future of Secure Login in 2026 Technology, Cyber Security, Online Safety Passkeys, Passwords, Passwordless Login, Cybersecurity 2026, Online Security, Google Passkeys, Apple Passkeys, Microsoft Security, Data Protection, Login Security Passkeys vs Passwords: Why Passkeys Are the Future of Secure Login in 2026 For decades, passwords have been the…
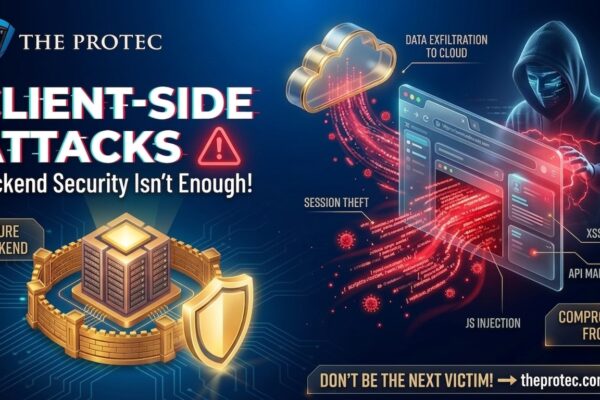
Explore the growing threat of client-side attacks, including browser exploits and frontend vulnerabilities like Magecart and script injection, and why backend security alone no longer suffices.

Discover why smartphone performance today hinges more on AI-driven processing than raw GHz, highlighting the role of NPUs and evolving mobile benchmarks.
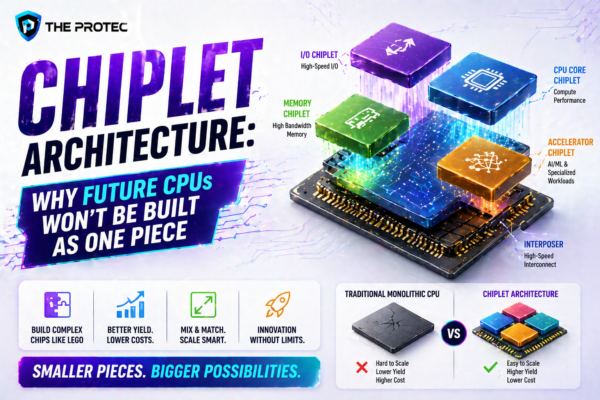
Discover how chiplet architecture is transforming CPU design by enhancing scalability, reducing costs, and increasing manufacturing flexibility through modular processors.

Explore how foldable phones have evolved in durability, pricing, and real-world usability to challenge traditional smartphones and shape the future.

Discover how shadow AI unauthorized AI tools used by employees poses significant security risks and what enterprises can do to combat this growing threat.

Discover how silicon-carbon batteries are revolutionizing smartphone battery tech by overcoming charging and capacity limits with cutting-edge battery innovation.

Explore the evolving techniques hackers use to exfiltrate data from cloud environments and discover effective data leak prevention strategies to safeguard your assets.
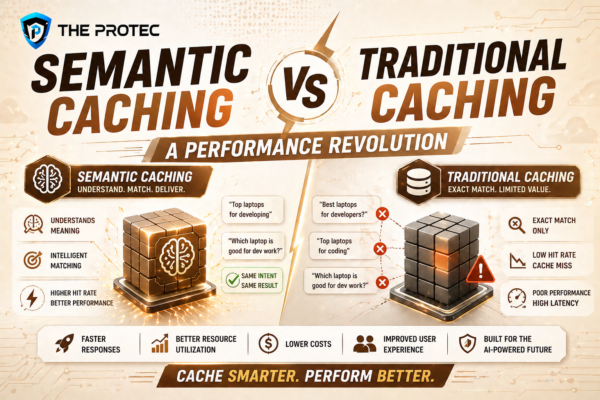
Explore how semantic caching redefines AI performance optimization and LLM caching compared to traditional methods, with benchmarks and implementation insights.