Introduction
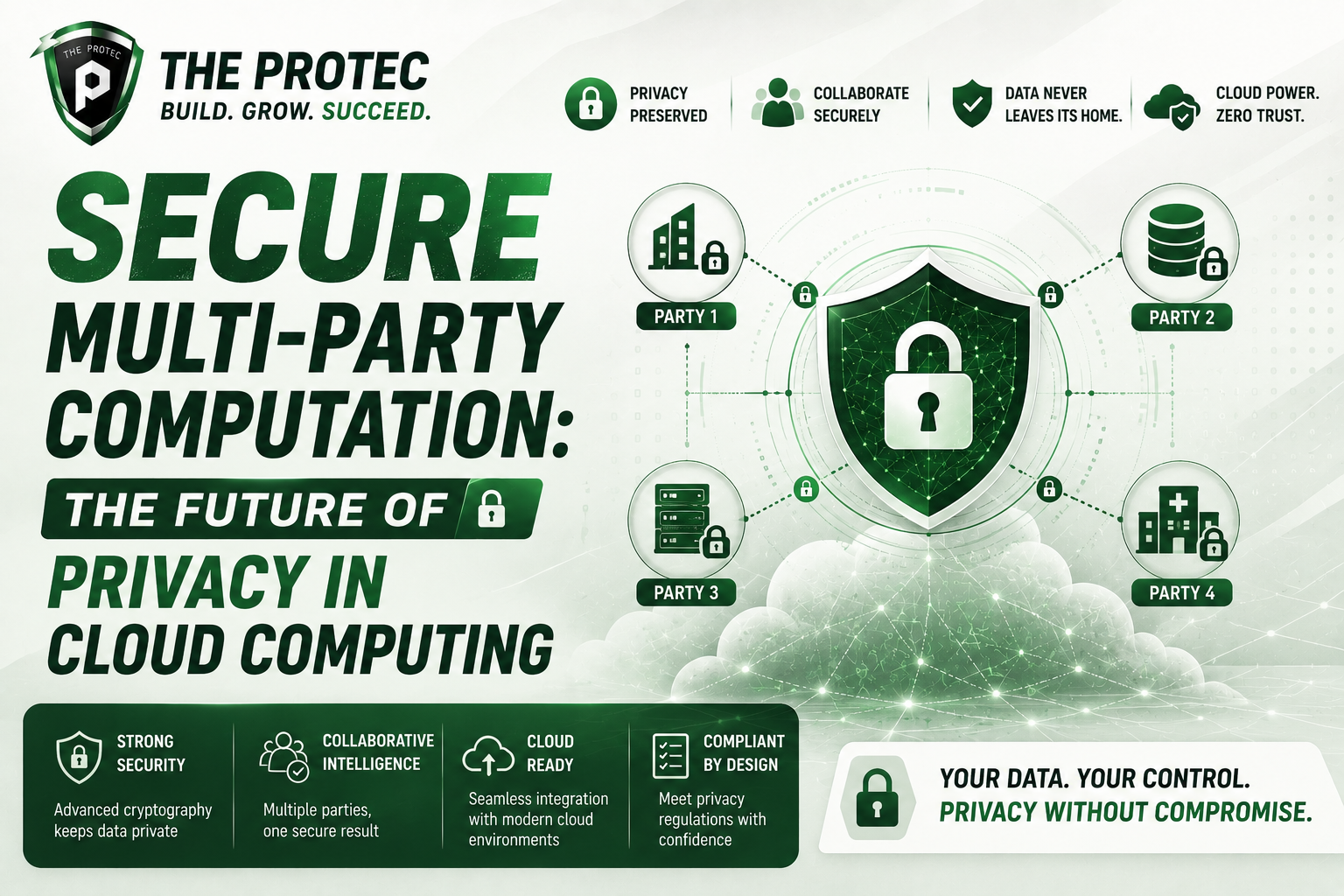
As cloud computing continues to dominate the digital landscape, protecting sensitive information while enabling collaboration is more critical than ever. Traditional methods of data protection, such as encryption and access control, often fall short when multiple parties need to jointly compute on private data without revealing it to one another. Enter secure multi-party computation (MPC): a groundbreaking privacy-preserving technology that allows parties to collectively perform computations on their combined data sets without exposing the underlying data itself. This article explores the fundamentals of secure computation, illuminates how MPC enhances data privacy in cloud environments, and dives into recent innovations shaping its trajectory in securing the future of cloud computing.
Understanding Secure Multi-Party Computation
Secure multi-party computation is a subset of cryptography designed to enable multiple participants to compute a function over their inputs while keeping those inputs private. Imagine several organizations wanting to collaborate on data analysis for example, financial institutions detecting fraud without sharing customer data among them. MPC lets these entities run joint computations on combined data safely without exposing their sensitive information to each other or outsiders.
How MPC Works in Simple Terms
At a high level, MPC protocols split sensitive data inputs into encrypted or secret-shared pieces distributed among multiple parties. These shares can be processed jointly to produce the computation’s result without any individual gaining access to the complete original data. In practice, the protocol involves cryptographic techniques like secret sharing schemes, homomorphic encryption, and oblivious transfer, among others. The process ensures:
- No single party can reconstruct the complete private data.
- The correctness of the computation is guaranteed.
- Data privacy is maintained even if some participants are malicious.
The Importance of Secure Computation in Cloud Environments
Cloud computing offers unmatched scalability and collaborative potential but raises critical concerns about data privacy. Organizations must place trust in cloud providers with their confidential data, which creates risks ranging from insider threats to data breaches. MPC counteracts these risks by enabling complex computations on encrypted or distributed data without exposing it– a perfect fit for cloud infrastructures keen on ensuring stringent data privacy requirements.
Benefits of MPC in Data Privacy Cloud Solutions
- Data confidentiality: Because raw data is never centrally revealed or decrypted during computation, data leakage risks vastly diminish.
- Regulatory compliance: MPC helps organizations comply with data protection regulations like GDPR and HIPAA that emphasize data minimization and confidentiality.
- Collaborative analytics: Multiple cloud tenants or business partners can jointly analyze data for insights without sharing underlying datasets.
- Reduced trust assumptions: Unlike traditional encryption-based cloud computing that requires trusting the cloud provider, MPC distributes trust among participants, lowering risk vectors.
Recent Developments and Trends in MPC Security
Advances in MPC protocols and computational power are making secure multi-party computation more practical and scalable than ever before. Here is a look at some current trends pushing MPC toward mainstream cloud adoption:
1. Efficient Protocols and Frameworks
New MPC protocols based on lattice-based cryptography, garbled circuits, and secret sharing have dramatically reduced computational overhead, making MPC suitable for real-time applications. Open-source frameworks like ENCRYPTO and MP-SPDZ provide accessible platforms for developers to integrate MPC into cloud solutions.
2. Integration with Trusted Execution Environments (TEEs)
Combining MPC with hardware-based TEEs, such as Intel SGX, improves performance and security by offloading part of the computation to secure enclaves. This hybrid approach enhances MPC security assurances against side-channel attacks and reduces latency.
3. Cross-cloud and Cross-organization Computations
As enterprises increasingly rely on multi-cloud and hybrid cloud architectures, MPC facilitates secure computations across disparate infrastructures and entities without exposing data, fostering innovation in federated learning and secure data markets.
Use Cases Demonstrating MPC in Cloud Privacy
Several industries are actively exploring MPC to address data privacy challenges within cloud environments.
Financial Services
Banks and insurers use MPC to collaboratively detect fraudulent transactions across institutions without revealing customer details. This collective analysis improves fraud prevention without compromising privacy.
Healthcare
MPC helps multiple hospitals or research institutions securely share patient data insights for large-scale medical research, enabling valuable discoveries while safeguarding protected health information.
Supply Chain Management
Companies share sensitive operational data to optimize logistics or detect inefficiencies without exposing proprietary information, enabled by MPC protocols running in the cloud.
Challenges and Future Outlook
Despite its promise, MPC technology continues to encounter hurdles that affect widespread adoption:
- Performance limitations: Although improved, MPC still demands higher computational resources compared to non-secure methods.
- Complexity of deployment: Implementing MPC requires specialized cryptographic expertise and integration effort.
- Standardization: The need for industry standards and interoperability remains crucial for cross-sector usability.
Nonetheless, ongoing research, coupled with growing awareness and demand for privacy-preserving cloud solutions, signals a robust outlook for MPC technology. As cloud computing shifts toward zero-trust architectures and privacy-by-design principles, MPC’s role as a critical enabler of secure computation and data privacy grows stronger.
FAQ: Secure Multi-Party Computation and Cloud Privacy
What is the difference between secure multi-party computation and traditional encryption?
Traditional encryption protects data at rest and in transit but requires decryption before processing, exposing data to potential breaches. Secure multi-party computation processes data while it remains encrypted or secret-shared, enabling computations without revealing the underlying data to any party, thus ensuring privacy throughout the lifecycle of data operations.
Can MPC be used with existing cloud services?
Yes, MPC protocols are increasingly designed to integrate with cloud infrastructures, either via standalone services specializing in privacy-preserving computation or as frameworks developers can deploy on cloud platforms. This integration enables organizations to enhance their cloud security posture without abandoning current cloud workflows.
How does MPC help comply with data privacy regulations?
MPC aligns with data protection regulations by minimizing the need to share or expose personal data in raw form. It enforces strong confidentiality guarantees, reduces attack surfaces, and supports purpose-specific data use, all of which are key principles in global data privacy laws like GDPR and HIPAA.
Conclusion
Secure multi-party computation represents a transformative leap forward in preserving data privacy amid growing reliance on cloud computing. By enabling collaborative computations without revealing sensitive inputs, MPC addresses fundamental privacy challenges inherent in modern cloud ecosystems. With ongoing advancements in protocol efficiency, hardware integration, and practical deployments across industries, MPC is poised to become a cornerstone technology in shaping secure, privacy-conscious cloud environments. For organizations navigating the complexities of data privacy, embracing MPC security offers a path toward unlocking collaborative potential without compromising confidentiality.
For more insights on implementing advanced privacy technologies, visit Cryptography Engineering.