Understanding Cloud Native Security Platforms (CNAPP)
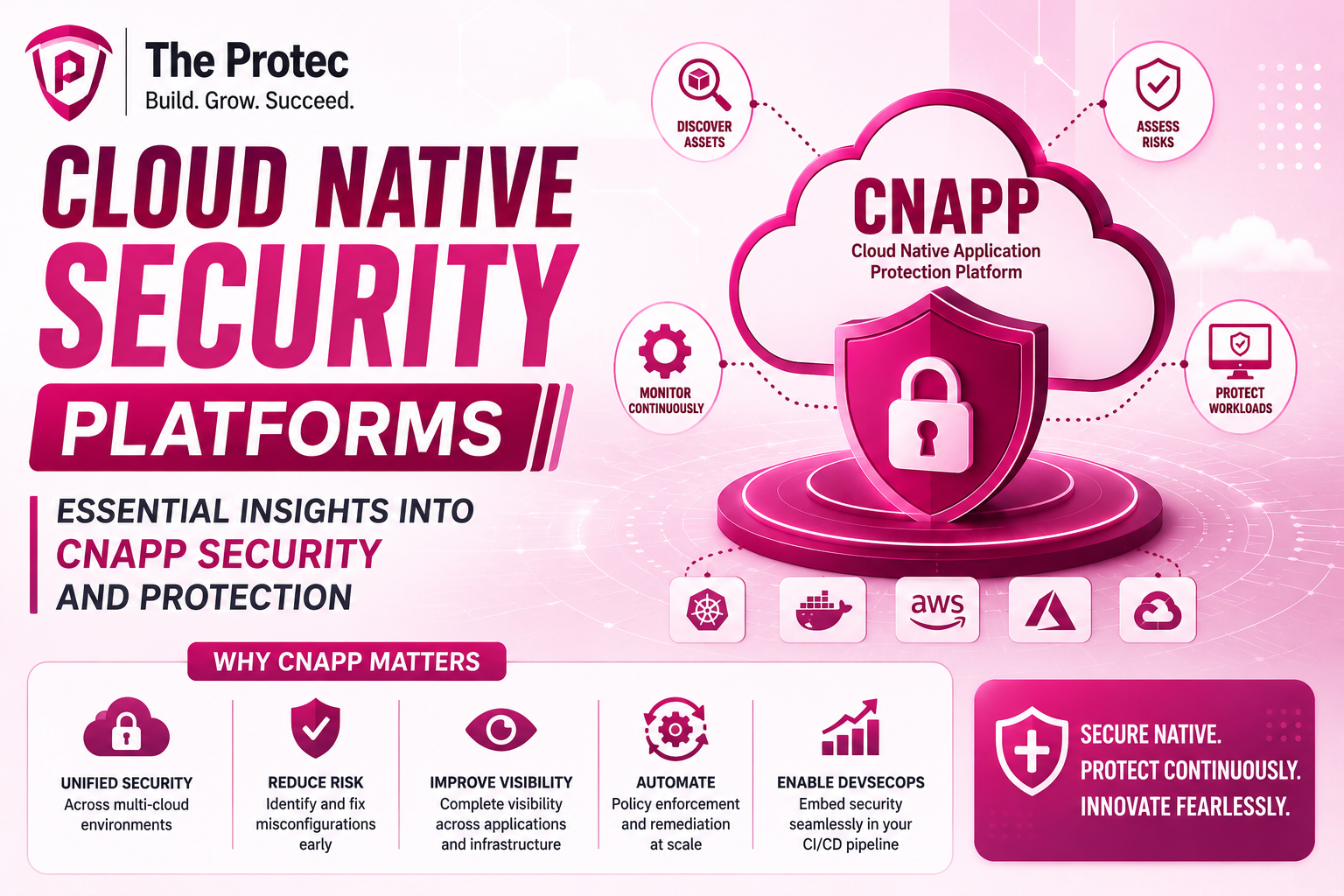
As organizations continue embracing cloud-first strategies, the security challenges in managing cloud environments have multiplied. Enter Cloud Native Security Platforms (CNAPP) an integrated approach designed specifically for securing cloud-native applications and infrastructure. These platforms unify various security functions to provide comprehensive visibility, risk management, and protection tailored for the complex, distributed nature of modern cloud environments.
Unlike traditional security tools that often operate in silos, CNAPPs enable enterprises to streamline their security posture across the development lifecycle and runtime environments. This evolving class of platforms addresses gaps left by conventional security by combining capabilities like cloud workload protection, posture management, and identity governance into one cohesive solution.
The Evolution of Cloud Native Security
Modern applications are built and deployed using containerization, microservices, and serverless architectures hosted within public, private, or hybrid clouds. This shift requires security models grounded in cloud-native principles agility, scalability, and automation. However, fragmented security tools can leave blind spots and increase risk.
Cloud protection platforms initially focused on securing workloads or cloud accounts separately. Over time, the rise of DevSecOps and Infrastructure as Code (IaC) sparked a need for integrated visibility and continuous security validation. CNAPP represents this maturation: a holistic platform where security data from cloud configurations, workloads, identities, and networks are correlated and analyzed.
Core Components and Capabilities of CNAPPs
Understanding the key components of a Cloud Native Security Platform helps clarify why these platforms are rapidly becoming indispensable.
1. Cloud Security Posture Management (CSPM)
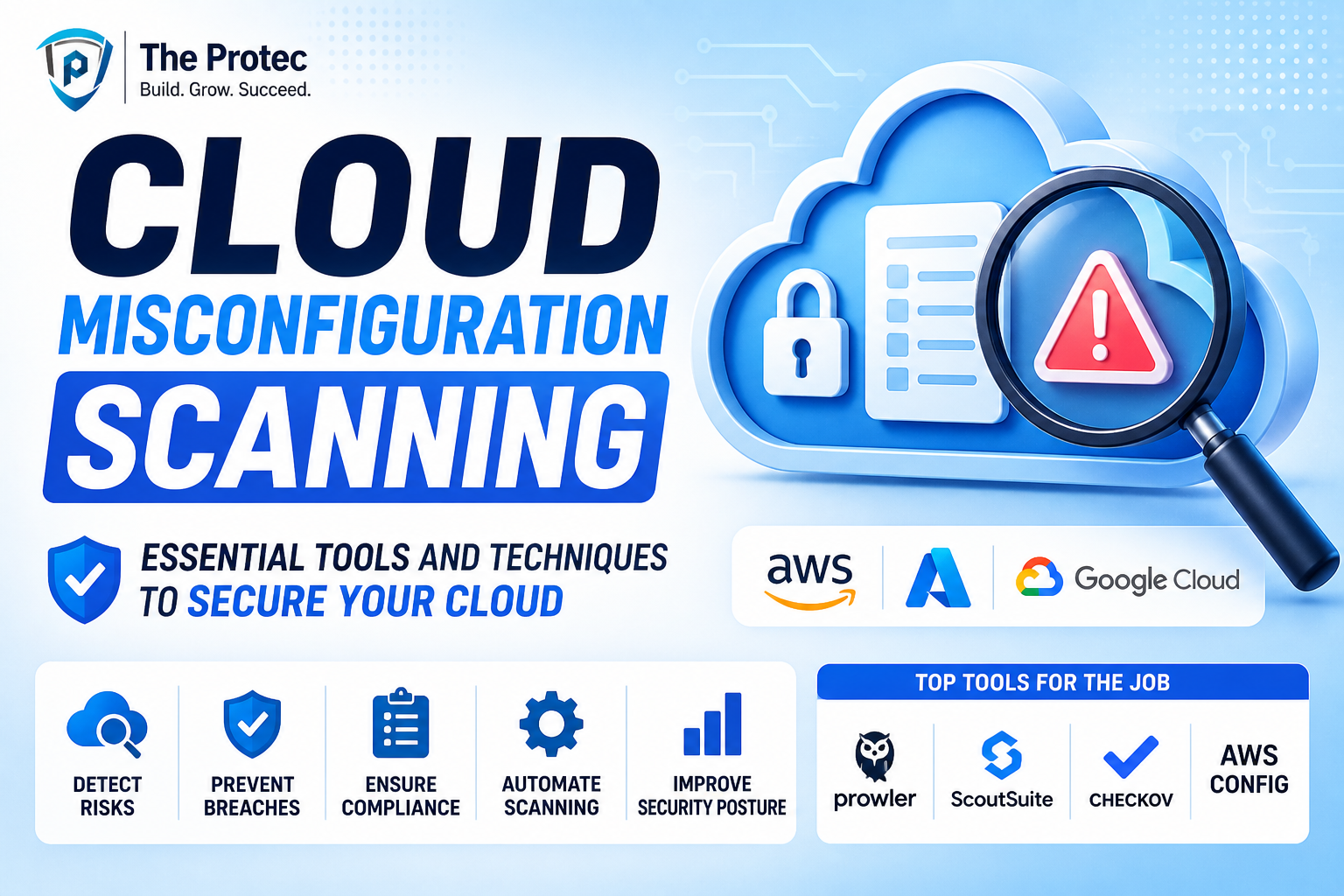
CSPM tools continuously monitor cloud environments to ensure compliance with security best practices and regulatory requirements. They identify misconfigurations and risky settings in cloud accounts and resources across providers like AWS, Azure, and Google Cloud. In the CNAPP framework, CSPM helps maintain a strong security baseline by automatically detecting configuration drift and vulnerabilities before they are exploited.
2. Cloud Workload Protection Platforms (CWPP)
CWPP solutions specialize in protecting workloads such as containers, virtual machines, and serverless functions. This includes real-time threat detection, runtime protection, vulnerability identification, and behavior analytics. By integrating CWPP within a CNAPP, organizations can enforce consistent protection policies and quickly remediate threats affecting dynamic workloads.
3. Infrastructure as Code (IaC) Security
Since infrastructure provisioning is often automated via IaC templates (e.g., Terraform, CloudFormation), securing those code artifacts is critical. CNAPPs incorporate IaC scanning to detect security flaws, compliance violations, or policy breaches before deployment effectively shifting security left and reducing risk introduction.
4. Identity and Access Management (IAM) Monitoring
Privilege mismanagement is a major vulnerability risk within cloud environments. CNAPP solutions monitor identities, roles, and entitlements to detect excessive permissions, anomalous behavior, and potential insider threats, enforcing least privilege principles.
5. Threat Intelligence and Detection
CNAPPs integrate threat intelligence feeds, behavioral analytics, and anomaly detection to identify indicators of compromise across cloud workloads and infrastructure. This capability allows for real-time incident response and proactive security posturing.
How CNAPP Enhances Cloud Native Security
Unified Visibility: Traditional tools produce fragmented visibility, making it difficult to understand cross-layer risks. CNAPP consolidates cloud data streams into a single pane, correlating findings from workload security, posture management, and IAM.
Automation and Continuous Security: CNAPP leverages automation to enforce compliance, perform vulnerability scans, and trigger alerts or remediation workflows. This ongoing security minimizes manual intervention and human error.
Improved DevSecOps Collaboration: By integrating IaC scanning and policy-as-code, CNAPP facilitates developer-friendly security feedback. Teams can remediate issues earlier in the development lifecycle, merging security with agile development seamlessly.
Scalability for Complex Environments: As multi-cloud adoption grows, maintaining consistent security is a challenge. CNAPPs are designed to scale across diverse environments, providing end-to-end coverage without added complexity.
Choosing the Right Cloud Protection Platform
With CNAPP emerging as a converged solution category, enterprises must evaluate offerings carefully. Key considerations include:
- Comprehensive Coverage: Does the CNAPP support multiple cloud providers, workloads, and security domains?
- Integration Capabilities: Can the platform integrate with existing DevOps and security tools for smooth workflows?
- Automation and Remediation: Does it provide automated enforcement and streamlined incident response?
- Usability and Analytics: How intuitive is the interface, and how actionable are the insights?
- Regulatory Compliance: Does it map security posture against audit frameworks like NIST, ISO, or PCI-DSS?
Some leading CNAPP providers also offer APIs and extensibility, allowing customization tailored to organizational policies and threat models.
Future Trends Impacting CNAPP Security
Cloud native security is a rapidly evolving field. Some key trends shaping CNAPP capabilities include:
- Integration of AI and ML: Advanced analytics enhance threat detection and automate response, reducing false positives and improving precision.
- Zero Trust Integration: CNAPPs are adopting zero trust principles, continuously verifying identities and device trust across cloud workloads.
- Extended Cloud-Native Coverage: Deeper visibility into emerging technologies like service mesh, edge computing, and container orchestration platforms (e.g., Kubernetes).
- Policy as Code Governance: Declarative policies embedded directly within CI/CD pipelines, enabling faster remediation and compliance assurance.
Frequently Asked Questions
1. How does CNAPP differ from traditional cloud security tools?
Traditional tools often address discrete security needs like endpoint protection or cloud account scanning in isolation. CNAPP integrates multiple security capabilities workload protection, posture management, IAM monitoring into a unified platform, offering holistic visibility and management in one place.
2. Can CNAPP tools secure multi-cloud and hybrid cloud environments?
Yes, one of CNAPP’s core strengths is its ability to provide consistent security across diverse cloud providers and hybrid deployments. This helps organizations maintain coherent policies and controls regardless of where workloads reside.
3. What role does automation play within CNAPP?
Automation is fundamental to CNAPP effectiveness. It enables continuous monitoring, automatic detection of misconfigurations and vulnerabilities, and even active response workflows that remediate issues without human intervention critical for scalable cloud security.
Conclusion
The rise of Cloud Native Security Platforms reflects a crucial evolution in securing modern digital infrastructure. As cloud environments become more distributed and dynamic, relying on siloed tools falls short of delivering the comprehensive protection enterprises require.
By converging multiple security functions into an integrated, automated solution, CNAPPs empower organizations to safeguard workloads, configurations, and identities with greater agility and effectiveness. Adopting a CNAPP strategy is no longer just an option but a necessary step toward achieving resilient, scalable cloud native security in today’s fast-paced digital landscape.
For further reading on cloud security best practices, visit the Cloud Security Alliance, a widely respected resource in cloud security governance and frameworks.