How to Buy Bitcoin: A Beginner’s Step-by-Step Guide
Learn how to buy Bitcoin with our step-by-step guide for beginners. Discover trusted exchanges, wallets, and tips to start your crypto journey.






Explore how foldable phones have evolved in durability, pricing, and real-world usability to challenge traditional smartphones and shape the future.

Discover how shadow AI unauthorized AI tools used by employees poses significant security risks and what enterprises can do to combat this growing threat.

Discover how silicon-carbon batteries are revolutionizing smartphone battery tech by overcoming charging and capacity limits with cutting-edge battery innovation.

Explore the evolving techniques hackers use to exfiltrate data from cloud environments and discover effective data leak prevention strategies to safeguard your assets.
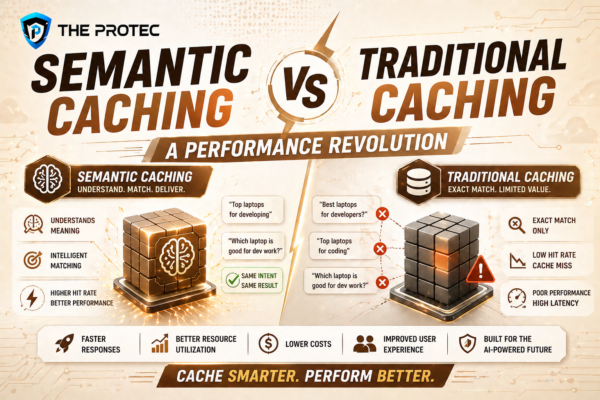
Explore how semantic caching redefines AI performance optimization and LLM caching compared to traditional methods, with benchmarks and implementation insights.
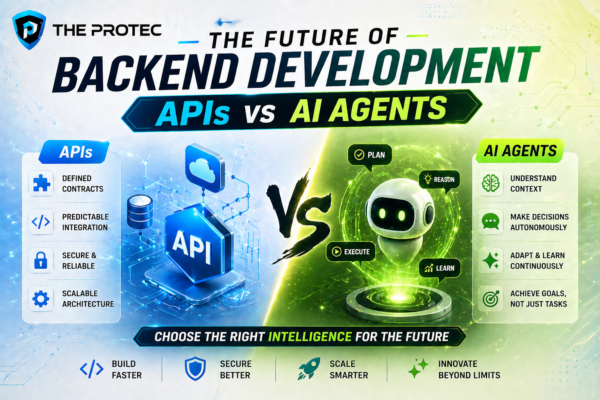
Explore the evolving landscape of backend development as we dissect if AI agents will replace traditional APIs and how agent-based architecture is shaping the future.

Discover how 2nm processors chips revolutionize mobile and laptop performance with enhanced efficiency, battery life, and heat management through advanced processor technology.

Explore how SSRF attacks exploit cloud metadata services, the critical cloud vulnerabilities they expose, and proven strategies to secure your infrastructure.
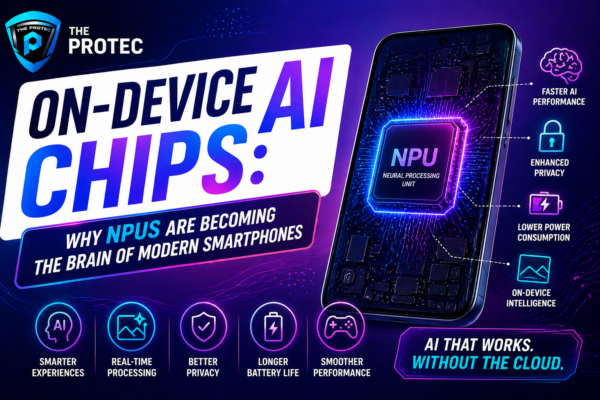
Discover how NPUs and on-device AI chips are revolutionizing smartphone performance by replacing cloud AI, ensuring faster, smarter, and more secure mobile experiences.

Learn Token Economics and explore the intricate relationship between AI token pricing, API rate limits, and how developers can optimize LLM cost control to avoid unexpected expenses.