Introduction
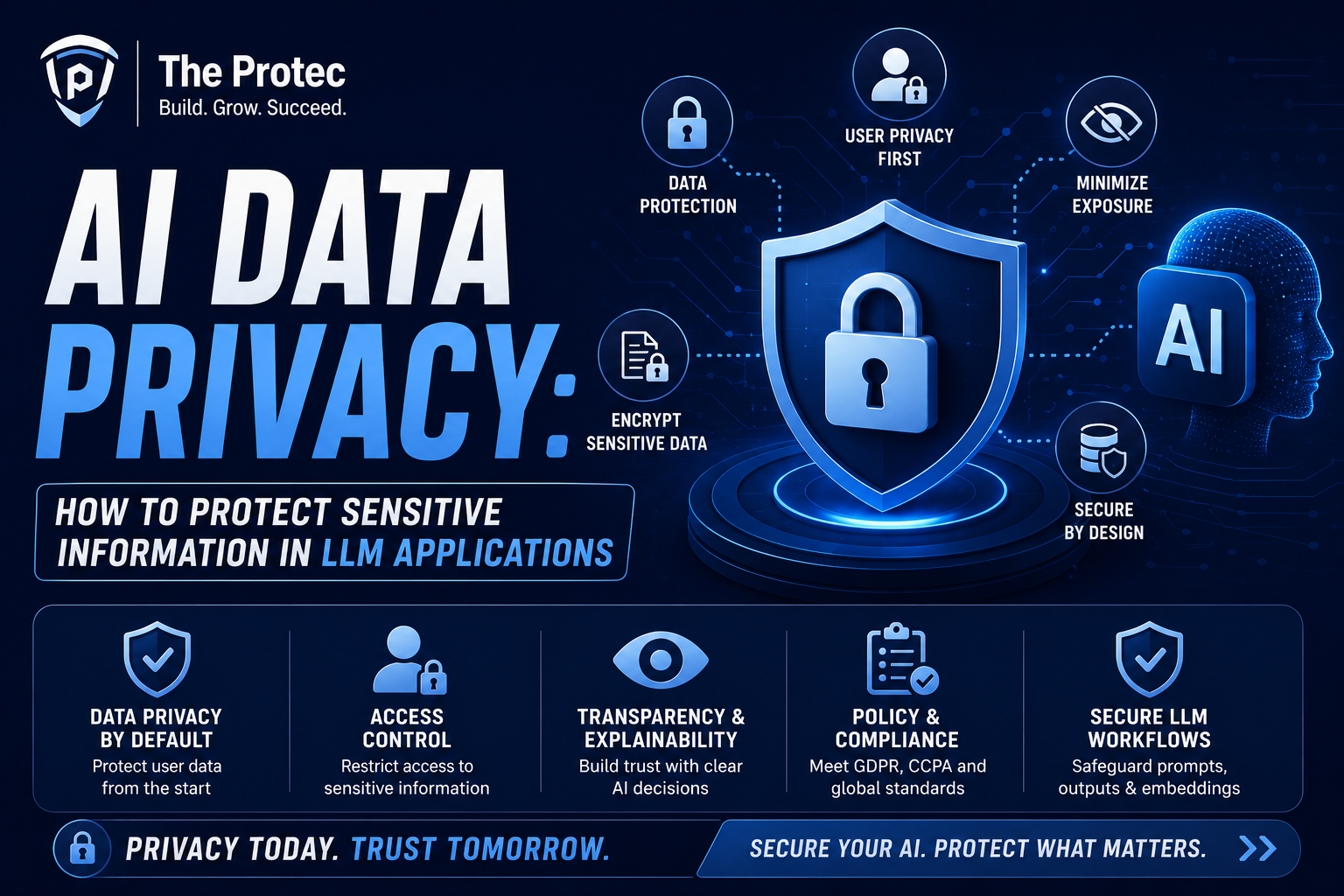
As large language models (LLMs) continue to revolutionize industries and redefine AI-driven communication, the privacy of sensitive data processed through these advanced applications has become a critical concern. The unprecedented scale and capability of LLMs bring with them complex challenges associated with data leakage, unauthorized access, and inadvertent exposure of confidential information. Effectively protecting sensitive data in AI applications is essential not only to satisfy compliance requirements but also to maintain user trust and data integrity in an increasingly connected digital environment.
This article delves into the emerging risks surrounding AI data privacy, specifically within LLM applications, and outlines best practices and mitigation strategies that organizations can implement to secure AI apps against threats.
The Growing Risks of Data Leakage in LLM Applications
Large language models, powered by massive datasets and complex algorithms, inherently pose privacy risks. These risks stem from how these models are trained, deployed, and queried.
1. Data Memorization and Unintended Disclosure
LLMs trained on vast corpora sometimes memorize and inadvertently reproduce sensitive snippets from their training data. This phenomenon, known as data leakage, can lead to exposure of personally identifiable information (PII), proprietary content, or confidential business data when users submit queries.
2. Inference Attacks
Adversaries may use crafted prompts to extract sensitive information held by the model, even if it wasn’t explicitly revealed during training. These inference attacks exploit subtle patterns or correlations that the model has internalized.
3. Data Handling in Deployment
Beyond training risks, data handled during inference — including user prompts and model responses — can contain sensitive content. Insecure APIs or inadequate encryption protocols can expose this data during transit or storage.
4. Third-Party and Cloud Exposure
Many LLM applications rely on cloud infrastructure and third-party services. Inadequate access controls, misconfigurations, or breaches at these external points can amplify risks of data leakage.
Strategies for Robust AI Data Privacy and LLM Data Protection
Addressing the privacy challenges in AI applications requires a multi-layered approach integrating technical, organizational, and procedural controls.
1. Data Minimization and Purpose Limitation
Minimize the collection and retention of sensitive data during both training and inference stages. Limit data usage strictly to what is necessary for model performance. By reducing the breadth of sensitive data inputs, organizations lower the attack surface.
2. Differential Privacy Techniques
Differential privacy injects calibrated noise into the training process to ensure that individual entries cannot be reliably extracted from the model. Employing these techniques can significantly help in preventing data memorization.
3. Federated Learning Approaches
Federated learning allows training models across decentralized devices or servers without exchanging sensitive datasets. This paradigm protects raw data by keeping it localized while updating the central model based on aggregated parameters.
4. Secure Model Serving and Access Controls
Implement strict authentication and authorization mechanisms for accessing AI APIs and model endpoints. Use role-based access control (RBAC) to limit user capabilities and avoid unauthorized queries that attempt to exploit the model.
5. Encryption in Transit and at Rest
All data communications involving LLM applications should be encrypted using up-to-date standards like TLS 1.3. Similarly, sensitive stored data, including logs and model checkpoints, must be encrypted to safeguard against unauthorized access.
6. Prompt and Response Filtering
Integrate content filtering to detect and redact sensitive or inappropriate information within user prompts and model outputs. This process helps prevent accidental or deliberate leakage of confidential information during interaction.
7. Continuous Monitoring and Auditing
Regularly audit logs and transaction histories to detect suspicious activities or anomalous queries indicative of data scraping or inference attacks. Employ anomaly detection tools to automatically flag potential threats.
8. Compliance with Privacy Regulations
Ensure AI application practices adhere to data protection laws such as GDPR, CCPA, and industry-specific standards. Legal compliance not only reduces liability but also enforces strong data governance principles.
Emerging Technologies Helping Secure AI Apps
Cutting-edge research is reinforcing AI data privacy through innovative tools and paradigms:
- Encrypted Inference: Techniques like homomorphic encryption enable models to perform computations on encrypted inputs, preventing exposure of sensitive data during inference.
- Secure Multiparty Computation (SMPC): Facilitates collaborative model training across parties without revealing private data to each other.
- Explainability and Model Interpretability: Transparent models allow auditors to detect risky behaviors such as data memorization and overfitting to sensitive information.
- Trustworthy AI Frameworks: Standards and certification for AI systems are emerging to ensure adherence to ethical data handling and privacy principles.
Best Practices for Organizations Deploying LLM Applications
Organizations must establish comprehensive policies and procedures to integrate these technologies and safeguards:
- Data Governance Framework: Define roles, responsibilities, and processes for data privacy management across AI teams.
- User Education and Awareness: Train developers and employees on privacy risks, secure coding practices, and compliance mandates.
- Model Lifecycle Management: Continuously evaluate models for privacy risks at every stage from training to deployment and retirement.
- Incident Response Plans: Prepare for potential data breaches or exploitation attempts with clear response strategies, mitigation steps, and communication protocols.
FAQ
What is the biggest privacy risk associated with LLMs?
The primary risk is data leakage, where the model inadvertently exposes sensitive information embedded in its training data or during inference, either by memorization or through exploitation by malicious users.
How does differential privacy improve AI data privacy?
Differential privacy adds controlled noise during the training process, obscuring the contribution of any single data point. This helps prevent the model from memorizing or revealing specific sensitive information.
Can cloud-based LLM services be fully secure?
While cloud providers invest heavily in security, complete protection depends on the correct implementation of access controls, encryption, and monitoring by the users. Organizations should employ strict security policies alongside cloud measures to secure sensitive data.
Conclusion
Ensuring AI data privacy in LLM applications is a multi-faceted challenge requiring technical innovations, procedural rigor, and vigilant monitoring. By understanding the risks of data leakage and applying comprehensive mitigation strategies like differential privacy, encrypted inference, and robust access controls, organizations can harness the powerful capabilities of LLMs while steadfastly protecting sensitive data. Adopting a culture of privacy-aware AI development will shape the future of secure AI apps and foster greater trust in intelligent systems deployed across industries.
For a deeper dive into secure AI practices and techniques, resources such as the NIST Privacy Engineering Program provide valuable guidelines and standards for developers and organizations.